
Translating complex regulatory requirements into a clear, actionable framework for continuous audit-readiness and peace of mind.
Guiding service organizations through the rigorous process of defining, implementing, and proving the internal controls necessary to achieve SOC 2 attestation and build client trust.
Adopting the industry’s gold standard for cybersecurity to build a robust, risk-based defense strategy tailored to your specific business profile and threats.

Implementing the strict technical and administrative safeguards required to protect electronic Protected Health Information (ePHI) and pass rigorous audits.
Our Compliance & Regulatory Support service demystifies complex frameworks like HIPAA, GLBA, and NIST, transforming anxiety into confidence. The pressure of compliance, from confusing regulations to the threat of fines, is immense. We act as your expert technology partner to make this manageable. We implement necessary technical safeguards using platforms like Microsoft Purview and Barracuda and provide guidance for risk assessments and due diligence. For formal audits, we partner with trusted professional firms for a complete, end-to-end solution.

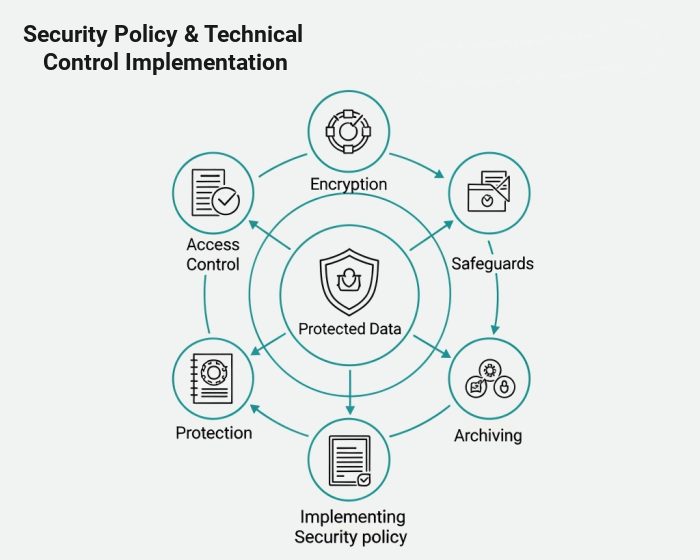
The ultimate value of our service is achieving a state of “continuous audit-readiness.” This empowers your business to operate with confidence, secure in the knowledge that you are protected from regulatory penalties and can prove your due diligence at a moment’s notice. It turns compliance from a burdensome cost center into a strategic asset that builds profound trust with your clients and stakeholders.
While the principles of good security are universal, the language of compliance is unique to each industry. Our expertise lies in our fluency with the specific mandates that govern your business, whether it’s protecting ePHI under HIPAA, securing financial data for GLBA, or meeting the rigorous standards of the ACC and NIST.
We help medical practices and healthtech companies navigate the complexities of HIPAA and HITECH. Our team implements the necessary technical safeguards to protect electronic Protected Health Information (ePHI), conducts required Security Risk Assessments, and ensures your infrastructure is prepared for rigorous audits.
We build the rigorous technical compliance frameworks required by the SEC, FINRA, and GLBA. From implementing immutable data archiving for communications to deploying advanced cybersecurity controls, we ensure your firm is ready to demonstrate continuous compliance during regulatory examinations.
We assist municipalities in securing critical public infrastructure and protecting citizen data against rising threats like ransomware. Our expertise includes implementing the strict technical controls necessary to achieve and maintain compliance with standards like CJIS for law enforcement data.
Upholding attorney-client privilege in the digital age requires robust technical defense. We secure your sensitive case data, manage strict access controls, and implement compliant communication platforms to ensure you meet your high ethical and professional obligations for confidentiality.
CPA firms face increasing pressure under the GLBA Safeguards Rule and strict IRS data security mandates. We implement the required technical security measures, multifactor authentication, and encryption to protect highly sensitive client financial data (PII) from breach and theft.
Regulatory pressure is increasing across every sector, driven by evolving state data privacy laws (like CCPA/CPRA) and stricter requirements from cyber insurance carriers. We help businesses of all types adopt recognized frameworks like NIST to build a defensible security posture, reduce organizational risk, and satisfy stakeholder demands for data protection.
No single solution stands alone in a modern business. True operational success is achieved when your infrastructure, security, and communications work together in perfect harmony. Explore how our related services integrate to build a resilient, future-proof foundation for your growth.
Transform your regulatory requirements into technical reality. We implement the rigorous, multi-layered cybersecurity defenses necessary to satisfy auditors and protect regulated data.
Modernize your governance strategy by leveraging the inherent security and compliance features of properly architected cloud platforms, such as Microsoft 365’s advanced data protection tools.
Compliance is a continuous state, not a one-time checkmark. Our proactive IT management ensures the daily operational discipline—like consistent patching and access controls—required to stay audit-ready.
